
Last August, academic researchers found a potent new method for knocking websites offline: a fleet of misconfigured servers additional than one hundred,000 sturdy that can amplify floods of junk information to as soon as-unthinkable sizes. These attacks, in several situations, could outcome in an infinite routing loop that causes a self-perpetuating flood of website traffic. Now, content material-delivery network Akamai says attackers are exploiting the servers to target websites in the banking, travel, gaming, media, and net-hosting industries.
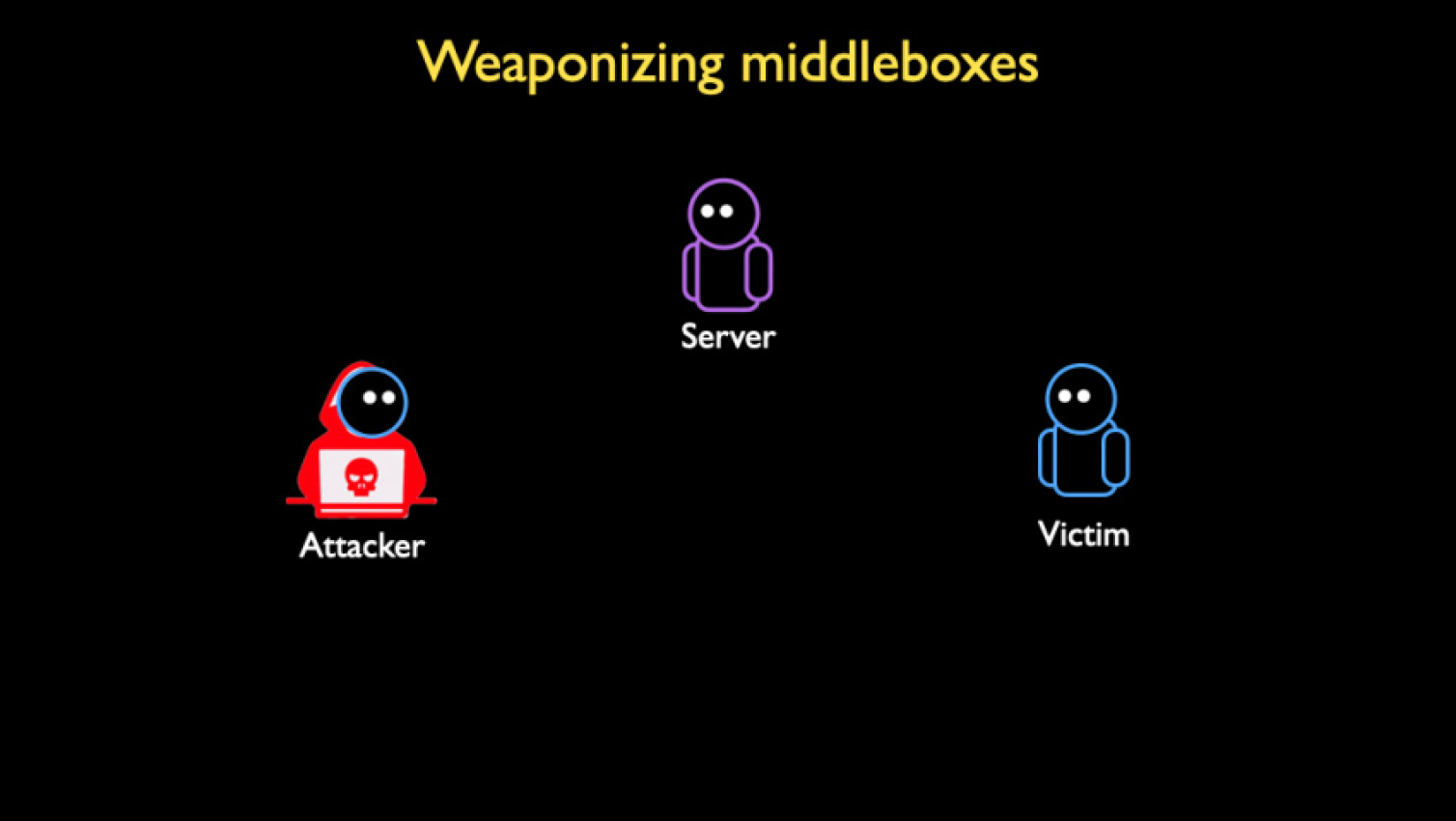
These servers—known as middleboxes—are deployed by nation-states such as China to censor restricted content material and by substantial organizations to block websites pushing porn, gambling, and pirated downloads. The servers fail to stick to transmission control protocol specifications that need a three-way handshake—comprising an SYN packet sent by the client, a SYN+ACK response from the server, followed by a confirmation ACK packet from the client—before a connection is established.
This handshake limits the TCP-primarily based app from becoming abused as amplifiers simply because the ACK confirmation need to come from the gaming firm or other target rather than an attacker spoofing the target’s IP address. But provided the want to manage asymmetric routing, in which the middlebox can monitor packets delivered from the client but not the final location that is becoming censored or blocked, several such servers drop the requirement by style.
A hidden arsenal
Last August, researchers at the University of Maryland and the University of Colorado at Boulder published research displaying that there had been hundreds of thousands of middleboxes that had the prospective to deliver some of the most crippling distributed denial of service attacks ever noticed.
For decades, folks have utilised DDoSes to flood websites with additional website traffic or computational requests than the websites can manage, denying solutions to reputable customers. DDoSes are related to the old prank of directing additional calls to the pizza parlor than the parlor has telephone lines to manage.
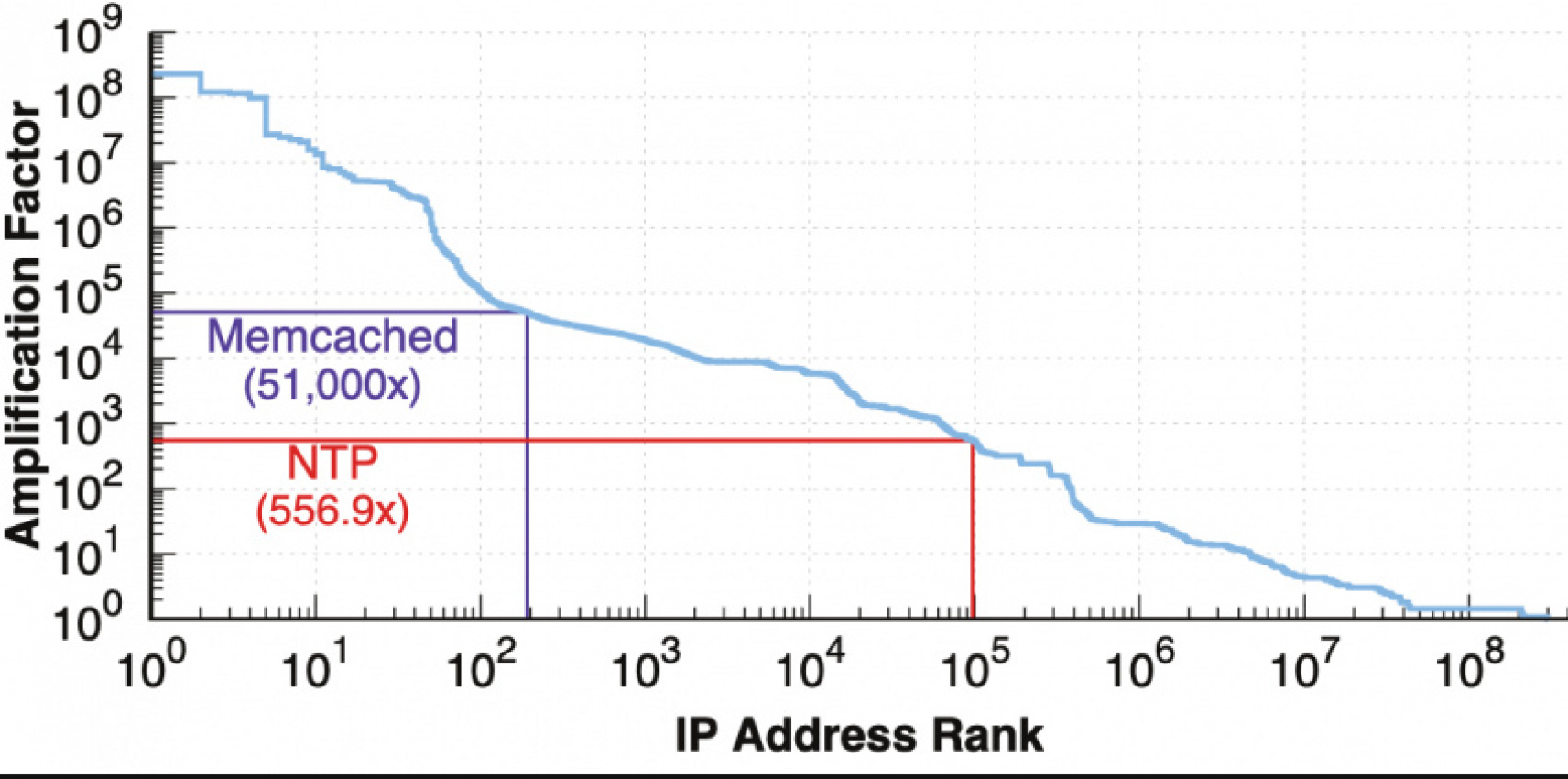
To maximize the harm and conserve sources, DDoSers typically enhance the firepower of their attacks although amplification vectors. Amplification operates by spoofing the target’s IP address and bouncing a fairly modest quantity of information at a misconfigured server utilised for resolving domain names, syncing personal computer clocks, or speeding up database caching. Because the response the servers automatically send are dozens, hundreds, or thousands of occasions larger than the request, the response overwhelms the spoofed target.
The researchers mentioned that at least one hundred,000 of the middleboxes they identified exceeded the amplification aspects from DNS servers (about 54x) and Network Time Protocol servers (about 556x). The researchers mentioned that they identified hundreds of servers that amplified website traffic at a larger multiplier than misconfigured servers using memcached, a database caching technique for speeding up sites that can enhance website traffic volume by an astounding 51,000x.
Here are two illustrations that show how the attacks perform:
Bock et al.
Day of reckoning
The researchers mentioned at the time that they had no proof of middlebox DDoS amplification attacks becoming utilised actively in the wild but anticipated it would only be a matter of time till that occurred.
On Tuesday, Akamai researchers reported that day has come. Over the previous week, the Akamai researchers mentioned, they have detected a number of DDoSes that utilised middleboxes precisely the way the academic researchers predicted. The attacks peaked at 11Gbps and 1.five million packets per second.
While modest when compared to the biggest DDoSes, each teams of researchers count on the attacks to get bigger as DDoSers start to optimize their attacks and recognize additional middleboxes that can be abused (the academic researchers didn’t release that information to stop it from becoming abused).
Kevin Bock, the lead researcher behind final August’s research paper, mentioned DDoSers had lots of incentives to reproduce the attacks his group theorized.
“Unfortunately, we weren’t shocked,” he told me upon studying of the active attacks. “We anticipated that it was only a matter of time till these attacks had been becoming carried out in the wild simply because they are simple and very productive. Perhaps worst of all, the attacks are new as a outcome, several operators do not however have defenses in location, which tends to make it that significantly additional enticing to attackers.”
One of the middleboxes received a SYN packet with a 33-byte payload and responded with a two,156-byte reply.
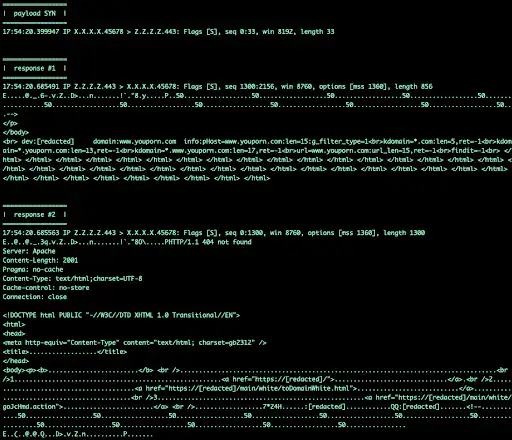
Akamai
That translated to a element of 65x, but the amplification has the prospective to be significantly higher with additional perform.
Akamai researchers wrote:
Volumetric TCP attacks previously necessary an attacker to have access to a lot of machines and a lot of bandwidth, usually an arena reserved for extremely beefy machines with higher-bandwidth connections and supply spoofing capabilities or botnets. This is simply because till now there wasn’t a considerable amplification attack for the TCP protocol a modest quantity of amplification was feasible, but it was deemed practically negligible, or at the extremely least subpar and ineffectual when compared with the UDP options.
If you wanted to marry a SYN flood with a volumetric attack, you would want to push a 1:1 ratio of bandwidth out to the victim, normally in the kind of padded SYN packets. With the arrival of middlebox amplification, this extended-held understanding of TCP attacks is no longer accurate. Now an attacker desires as small as 1/75th (in some situations) the quantity of bandwidth from a volumetric standpoint, and simply because of quirks with some middlebox implementations, attackers get a SYN, ACK, or PSH+ACK flood for totally free.
Keyword: DDoSers are using a potent new method to deliver attacks of unthinkable size
