
A malicious app downloaded from Google Play more than 10,000 times surreptitiously installed a remote access trojan that stole users’ passwords, text messages, and other confidential information, a safety firm reported.
The trojan, which goes below the names TeaBot and Anatsa, came to light last May. It utilised streaming software program and abused Android’s accessibility solutions in a way that permitted the malware creators to remotely view the screens of infected devices and interact with the operations the devices carried out. At the time, TeaBot was programmed to steal information from a predefined list of apps from about 60 banks about the globe.
On Tuesday, safety firm Cleafy reported that TeaBot was back. This time, the trojan spread by way of a malicious app known as QR Code & Barcode Scanner, which as the name recommended, permitted customers to interact with QR codes and barcodes. The app had more than 10,000 installations prior to Cleafy researchers notified Google of the fraudulent activity and Google removed it.
“One of the greatest distinction[s], compared to the samples found for the duration of… May 2021, is the enhance of targeted applications which now consist of household banking applications, insurances applications, crypto wallets, and crypto exchanges,” Cleafy researchers wrote. “In much less than a year, the quantity of applications targeted by TeaBot have grown more than 500%, going from 60 targets to more than 400.”
In current months, TeaBot also began supporting new languages like Russian, Slovak, and Mandarin Chinese to show custom messages on infected phones. The fraudulent scanner app distributed on Play was detected as malicious by only two antimalware solutions, and it requested only a handful of permissions at the time it was downloaded. All the critiques portrayed the app as reputable and properly-functioning, producing TeaBot tougher for much less knowledgeable individuals to recognize as a danger.
Once installed, the malicious QR Code & Barcode Scanner app displayed a pop-up informing customers that an update was obtainable. But rather than producing the update obtainable by way of Play as is standard, the pop-up downloaded it from two particular GitHub repositories designed by a user named feleanicusor. The two repositories, in turn, installed TeaBot.
This graph offers an overview of the infection chain created by the TeaBot authors:
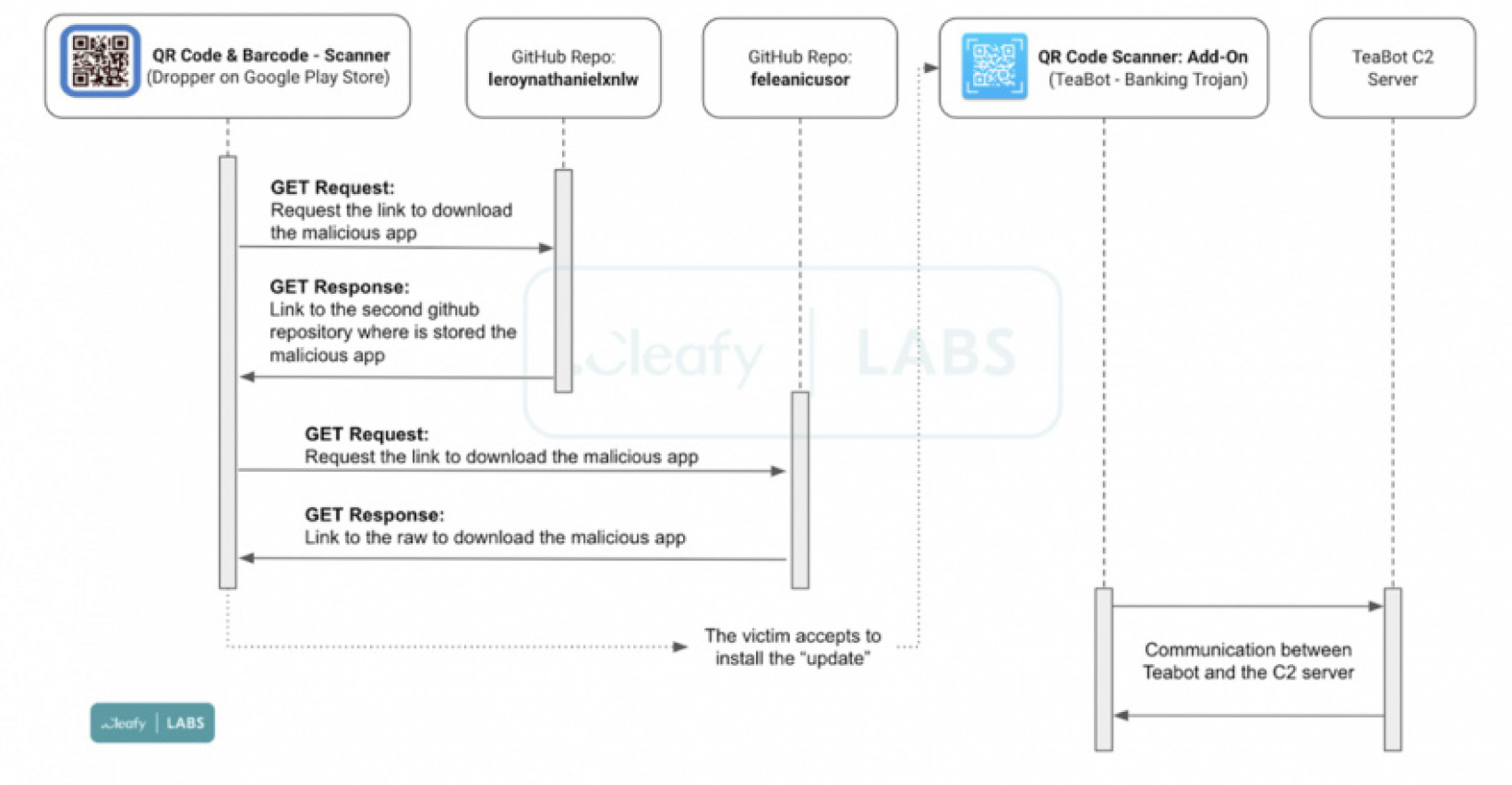
Cleafy
Cleafy researchers wrote:
Once the customers accept to download and execute the fake “update”, TeaBot will commence its installation approach by requesting the Accessibility Services permissions in order to receive the privileges necessary:
- View and manage screen: utilised for retrieving sensitive data such as login credentials, SMS, 2FA codes from the device’s screen.
- View and carry out actions: utilised for accepting distinct types of permissions, right away right after the installation phase, and for performing malicious actions on the infected device.
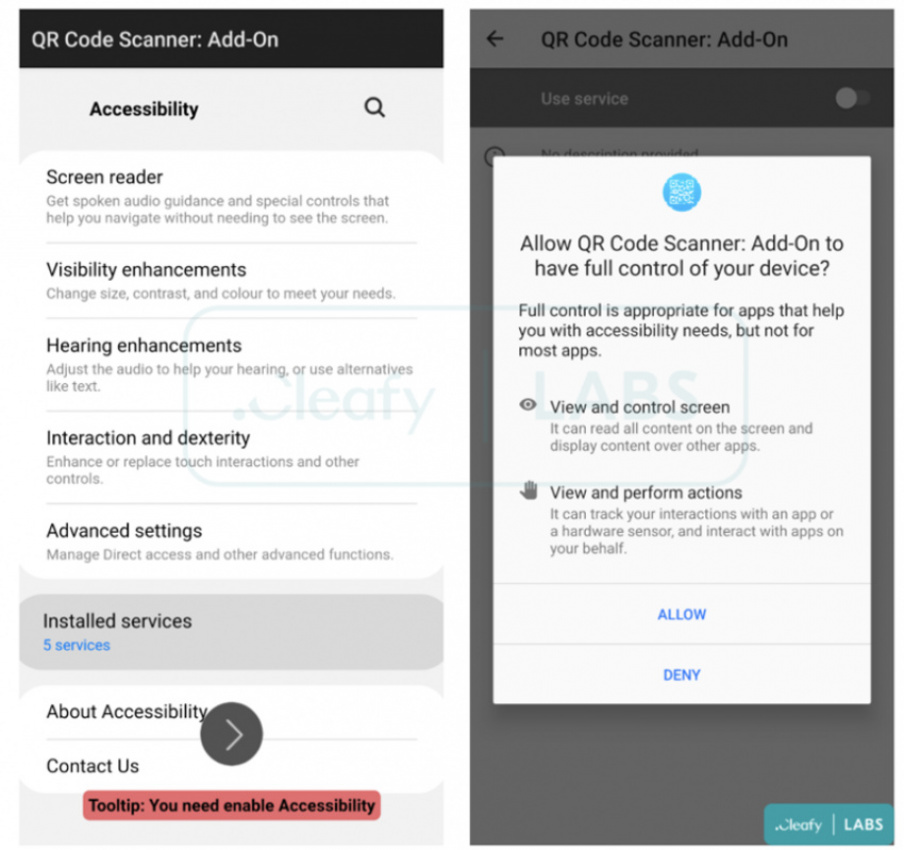
Cleafy
TeaBot is only the most recent piece of Android malware to be spread by way of Google’s official app market place. The business is usually rapid to take away malicious apps after they’re reported, but it continues to struggle to determine malware on its personal. Google representatives didn’t respond to an e-mail looking for comment for this post.
Tuesday’s post from Cleafy has a list of indicators that individuals can use to figure out if they installed the malicious app.
Listing image by Getty Images
Keyword: Google Play app downloaded more than 10,000 times contained data-stealing RAT
